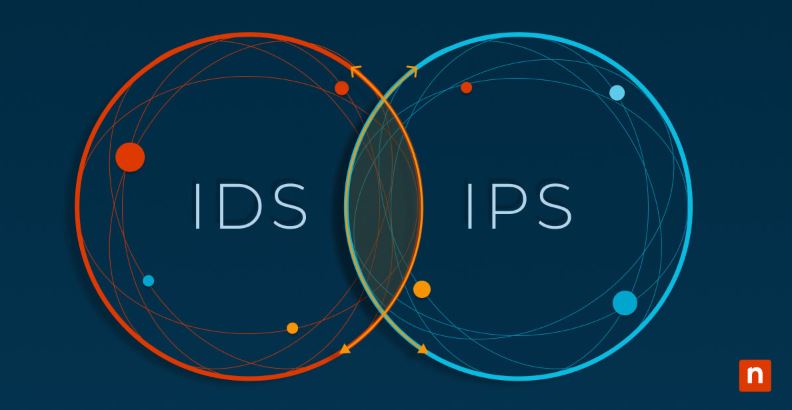
With the rise of cyber threats, organizations need advanced security solutions. Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) are two essential tools for protecting networks and systems. This article explains their definitions, how they work, and the key differences between them.
What is an Intrusion Detection System (IDS)?
1. Definition of IDS
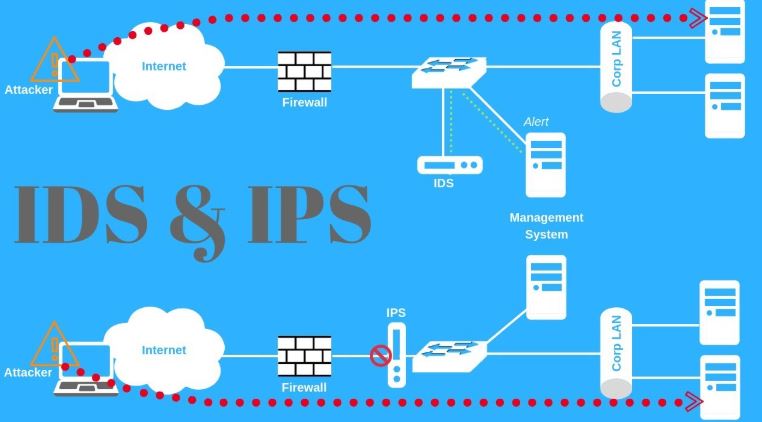
An Intrusion Detection System (IDS) is a security tool that monitors network traffic or system activities to detect potential threats or malicious behavior.
2. How IDS Works
- Data Collection: Monitors network traffic.
- Data Analysis: Compares detected patterns with a database of known threats.
- Alert Generation: Sends alerts to security administrators when suspicious activity is found.
3. Types of IDS
- Network-based IDS (NIDS): Monitors network traffic.
- Host-based IDS (HIDS): Analyzes activities on individual devices.
4. Advantages of IDS
✅ Helps identify threats before significant damage occurs.
✅ Provides detailed analysis of suspicious activities.
✅ Enhances security policies.
5. Disadvantages of IDS
❌ Cannot prevent attacks—only detects and alerts.
❌ May generate false positives.
What is an Intrusion Prevention System (IPS)?
1. Definition of IPS
An Intrusion Prevention System (IPS) is a security tool that detects and blocks suspicious activities before they cause harm.
2. How IPS Works
- Traffic Monitoring: Analyzes network traffic like IDS.
- Automated Response: Blocks attacks or disconnects malicious connections.
3. Types of IPS
- Network-based IPS (NIPS): Operates at the network level.
- Host-based IPS (HIPS): Protects individual devices.
4. Advantages of IPS
✅ Automatically blocks threats.
✅ Provides real-time network protection.
✅ Reduces workload for security teams.
5. Disadvantages of IPS
❌ If misconfigured, it may block legitimate traffic.
❌ May introduce slight network latency.
Key Differences Between IDS and IPS
| Criteria | IDS (Intrusion Detection System) | IPS (Intrusion Prevention System) |
|---|---|---|
| Function | Monitors and alerts only | Monitors and blocks attacks |
| Interaction | Passive (does not take action) | Active (takes preventive action) |
| Threat Handling | Detects threats only | Prevents threats in real-time |
| Impact on Traffic | No impact on data flow | Can influence network performance |
| Alerts | Sends alerts to administrators | Blocks threats automatically |
Why Do You Need IDS or IPS?
1. Strengthening Network Security
🔹 IDS provides visibility into suspicious activities.
🔹 IPS acts as the first line of defense against attacks.
2. Compliance with Security Standards
✅ IDS and IPS are essential for compliance with PCI DSS, ISO 27001, and other security regulations.
3. Real-Time Protection
🚀 IPS enables immediate response to cyber threats.
Use Cases of IDS and IPS
1. IDS Use Cases
✔️ Monitoring suspicious activities in network traffic.
✔️ Analyzing past attacks to improve security policies.
2. IPS Use Cases
✔️ Blocking attacks in real-time before they cause harm.
✔️ Protecting critical networks from targeted threats.
Challenges of Using IDS and IPS
1. False Positives
⚠️ IDS and IPS may generate false alerts, wasting time on non-threats.
2. Performance Issues
⚠️ IPS can slow down network performance if not configured properly.
3. Configuration & Maintenance
⚠️ Continuous tuning is required to balance security and functionality.
Conclusion
IDS and IPS are crucial cybersecurity solutions for protecting networks and systems. While IDS focuses on detecting threats and sending alerts, IPS actively blocks attacks in real-time. Choosing the right system depends on an organization’s security needs and the level of protection required.