Social engineering is one of the most effective techniques used by cyber attackers. Instead of hacking systems through software vulnerabilities, social engineering exploits human psychology to gain access to sensitive information. In this article, we will explore the concept of social engineering in cybersecurity, its methods, and the best ways to protect against it.
What is Social Engineering?
1. Definition of Social Engineering
- Social engineering in cybersecurity refers to the psychological manipulation of victims to obtain confidential information or gain access to secure systems.
- Instead of using complex technical methods, attackers rely on deception and trust exploitation.
2. Primary Objectives
- Acquiring sensitive data such as passwords, bank account details, or classified information.
- Gaining access to critical systems within organizations.
Common Social Engineering Techniques in Cybersecurity
1. Phishing
How It Works:
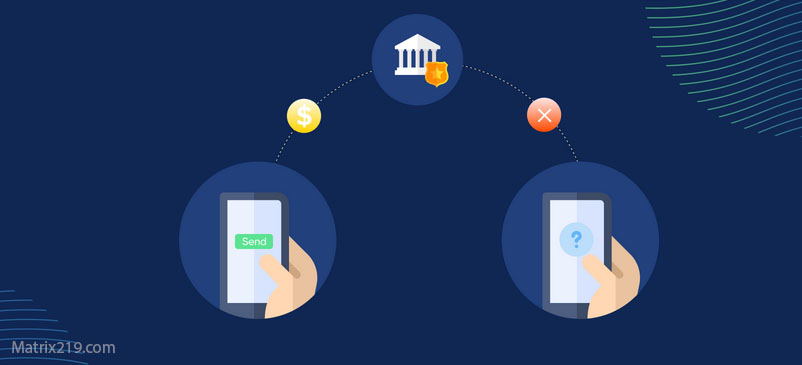
- Attackers send emails that appear to be from legitimate sources, such as banks or companies.
- The goal is to trick victims into clicking malicious links or providing login credentials.
Example:
- An email claiming that your bank account has been frozen, urging you to update your details via a fake link.
2. Spear Phishing
How It Works:
- Attackers send highly personalized emails, containing specific information about the victim.
- The aim is to increase credibility and success rates.
Example:
- An email directed at an employee requesting confidential company data.
3. Voice Phishing (Vishing)
How It Works:
- Attackers call victims, pretending to be from a trusted entity, such as a bank or tech support.
- The objective is to trick victims into revealing sensitive information.
Example:
- A call from “customer support” asking you to confirm your bank card details.
4. Physical Social Engineering
How It Works:
- Attackers gain unauthorized access to office buildings to steal documents or electronic devices.
Example:
- Posing as an IT technician to gain entry into a company’s server room.
5. Social Media Exploitation
How It Works:
- Attackers collect information about victims from their social media profiles.
- This data is then used for phishing attacks or identity theft.
Example:
- Discovering your pet’s name from Facebook posts and using it to bypass security questions.
Real-World Examples of Social Engineering Attacks
1. Twitter Hack (2020)
What Happened:
- Attackers targeted Twitter employees with phishing messages, gaining access to high-profile accounts.
Result:
- Fraudulent tweets were posted to solicit cryptocurrency payments.
2. Target Data Breach (2013)
What Happened:
- Social engineering was used to obtain login credentials from a third-party vendor.
Result:
- Millions of customer records were compromised.
Risks of Social Engineering Attacks
1. Risks for Individuals
- Identity theft and personal data exposure.
- Financial losses due to fraud.
2. Risks for Organizations
- Unauthorized access to sensitive company information.
- Financial losses and reputational damage.
How to Protect Against Social Engineering in Cybersecurity
1. Awareness and Training
- Educate employees and individuals on how to recognize social engineering attacks.
- Conduct regular cybersecurity awareness workshops.
2. Use Two-Factor Authentication (2FA)
- Adds an extra security layer to make unauthorized access more difficult.
3. Limit Publicly Available Information
- Reduce sharing of personal details on social media platforms.
4. Analyze Emails and Links
- Always verify the source before clicking links or providing personal data.
5. Implement Strict Security Policies
- Enforce policies that prevent sharing passwords or confidential data via email or phone.
6. Deploy Security Software
- Use antivirus programs and anti-phishing tools for added protection.
How Organizations Can Combat Social Engineering
1. Build a Strong Security Culture
- Make cybersecurity awareness an integral part of company culture.
2. Leverage AI Security Tools
- Use AI-based tools to analyze user behavior and detect threats early.
3. Rapid Incident Response
- Develop emergency response plans to quickly contain and mitigate cyberattacks.
Conclusion
Social engineering is one of the most dangerous threats in cybersecurity because it exploits human trust rather than system vulnerabilities. By raising awareness, enforcing strict security policies, and utilizing modern security technologies, individuals and organizations can minimize the risks of these attacks.
For further insights, visit the original article at: Matrix219.Net