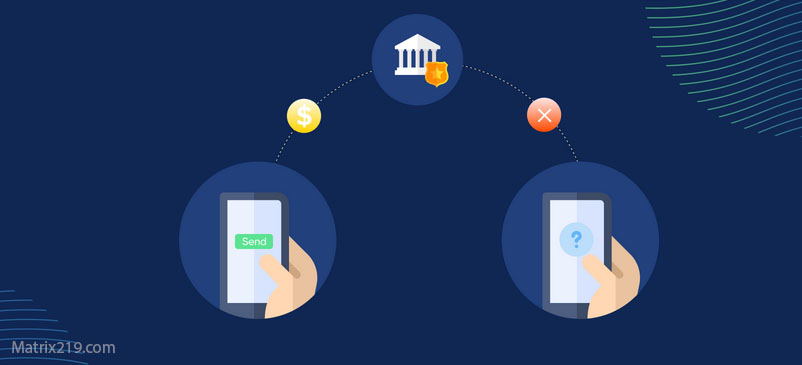
Social engineering attacks are among the most dangerous cyber threats that exploit human psychology rather than technical vulnerabilities. Cybercriminals use manipulation tactics to trick individuals into revealing sensitive information or taking harmful actions.
Here are 9 essential steps to protect yourself from social engineering attacks:
1️⃣ Verify the Sender’s Identity
Before providing any personal information or following any request, ensure the sender is legitimate. Double-check emails, phone numbers, and message sources.
2️⃣ Confirm the Source Before Sharing Information
If an unknown person contacts you requesting sensitive details (such as passwords or financial data), verify their identity before disclosing any information. If in doubt, hang up or ignore the request.
3️⃣ Limit Personal Information Sharing on Social Media
🔹 Avoid sharing sensitive details such as your address, workplace, or financial data online.
🔹 Hackers can use these details for phishing attacks or identity theft.
4️⃣ Use Strong Passwords and Enable Two-Factor Authentication (2FA)
🔹 Create complex and unique passwords for each account.
🔹 Enable 2FA to add an extra layer of security.
5️⃣ Keep Software and Applications Updated
🔹 Cybercriminals exploit security vulnerabilities in outdated systems.
🔹 Regularly update your operating system, antivirus software, and web browsers to stay protected.
6️⃣ Increase Awareness and Stay Educated
🔹 Learn about different types of social engineering attacks and how to recognize them.
🔹 Consider attending cybersecurity training if available.
7️⃣ Avoid Clicking on Suspicious Links and Messages
🔹 Do not click on unknown links in emails or messages.
🔹 Always verify URLs before visiting a website.
8️⃣ Regularly Backup Your Data
🔹 Maintain secure and encrypted backups of important files.
🔹 Use cloud storage or external drives for added security.
9️⃣ Consult Cybersecurity Experts When Needed
🔹 If you suspect an attack or need cybersecurity advice, seek professional assistance to assess risks and implement protective measures.
Source:
📌 Read the full article: How to Protect Yourself from Social Engineering Attacks