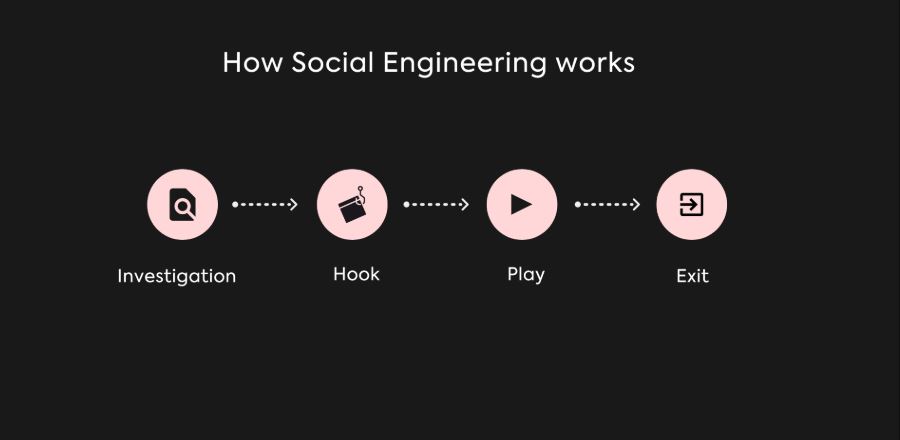
Social engineering is the art of psychological manipulation used to extract sensitive information or conduct cyberattacks. This process relies on exploiting trust and human relationships, following a structured methodology to achieve its objectives. In this article, we will explore the key stages of social engineering and how attackers operate to reach their goals, as outlined in Social Engineering: The Complete Guide to Human-Based Cyber Attacks.
Stages of Social Engineering
1. Information Gathering (Reconnaissance)
Description:
Attackers begin by collecting as much information as possible about the target. This stage focuses on understanding the victim’s digital footprint, habits, and social connections before any direct interaction takes place.
Sources include:
Search engines, social media platforms, and publicly available records. Excessive data exposure, often discussed in Digital Privacy and Online Tracking: How You’re Tracked Online and How to Protect Yourself, significantly increases the effectiveness of this phase.
Common Techniques:
-
Google Dorking (advanced search queries)
-
Analyzing social media accounts
-
Using tools like Maltego for data mapping
Objective:
Understanding the victim’s behavior, vulnerabilities, and social connections.
2. Building Trust
Description:
Attackers establish trust with the victim through direct or indirect interaction. They may impersonate a friend, colleague, or trusted organization such as a bank or service provider.
Common Techniques:
-
Sending emails that appear legitimate
-
Making targeted phone calls
-
Engaging with victims on social media
These trust-building tactics closely mirror the manipulation patterns explained in The Psychology Behind Social Engineering Attacks.
Objective:
Make the target comfortable enough to share information or perform requested actions.
3. Exploitation
Description:
Once trust is established, the attacker exploits the victim to gain access to sensitive data or systems. This is the most critical phase, where manipulation turns into direct compromise.
Common Techniques:
-
Phishing: Sending fake login pages
-
Spear Phishing: Personalized phishing emails
-
Physical Social Engineering: Gaining physical access to secured areas
Many of these methods are broken down in detail in Phishing as a Social Engineering Technique.
Objective:
Compromise systems or obtain confidential data.
4. Execution
Description:
The attacker uses the acquired information to complete their final objective, such as data theft, financial fraud, or launching cyberattacks.
Examples:
-
Transferring funds based on fraudulent requests
-
Using stolen credentials to infiltrate systems
-
Blackmailing victims with compromised data
This stage often overlaps with broader account compromise scenarios covered in Account Security and Recovery – How to Recover Hacked Accounts Legally.
Objective:
Leverage stolen information for personal or financial gain.
5. Covering Tracks
Description:
After completing the attack, the perpetrator takes steps to erase evidence that could expose their identity. This includes deleting communication records, masking IP addresses, and altering digital traces.
Objective:
Minimize the chances of detection and legal consequences.
Real-World Examples of Social Engineering Attacks
1. Target Data Breach (2013)
-
Phase 1: Attackers gathered intelligence on a third-party vendor
-
Phase 2: Phishing emails were sent to vendor employees
-
Phase 3: Stolen credentials enabled network access
-
Phase 4: Millions of customer records were compromised
2. Twitter Hack (2020)
-
Phase 1: Attackers researched Twitter’s support team
-
Phase 2: Vishing (voice phishing) was used to manipulate employees
-
Phase 3: Access was gained to high-profile accounts
These incidents clearly demonstrate how structured social engineering stages are applied in real environments.
How to Defend Against Social Engineering Attacks
1. User Awareness & Training
Educate employees and individuals about social engineering techniques and the risks of oversharing information online, a core focus of Protection Against Social Engineering: A Comprehensive Guide for Individuals and Organizations.
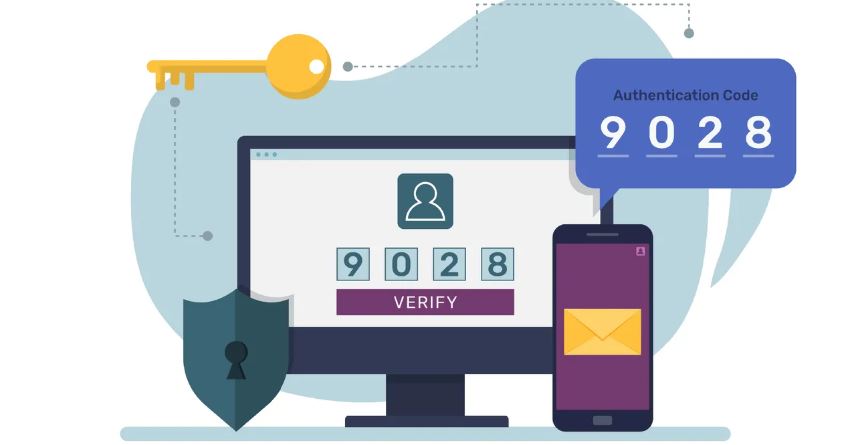
2. Implement Security Measures
-
Enable two-factor authentication (2FA)
-
Use antivirus and anti-phishing tools
3. Limit Publicly Available Information
-
Reduce exposure of personal data on social platforms
-
Regularly review privacy settings
4. Establish Strong Security Policies
-
Prohibit sharing sensitive data via email or phone
-
Enforce strict verification procedures
Conclusion
Understanding the stages of social engineering helps individuals and organizations recognize and counter manipulation tactics more effectively. By combining awareness, technical safeguards, and clear security policies, the risks posed by social engineering attacks can be significantly reduced.
For broader conceptual context, see Encyclopaedia Britannica – Social Engineering.