In the digital age, social engineering has become one of the most dangerous threats to individuals and organizations. Instead of relying on technical exploits, attackers manipulate human psychology to gain unauthorized access to sensitive information. This article explores the concept of social engineering, its significance, common attack methods, and how to protect against it.
What is Social Engineering?
1. Definition
Social engineering refers to manipulative techniques used by attackers to deceive individuals into revealing sensitive information or granting unauthorized system access.
2. How It Works
- Attackers exploit human trust and emotions to gather confidential data.
- They create convincing scenarios to persuade victims to take specific actions.
3. Why is it Dangerous?
- Bypasses traditional security measures like antivirus software and firewalls.
- Targets the human element, which is often the weakest link in cybersecurity.
Importance of Understanding Social Engineering
For Organizations:
- Protecting assets – Helps reduce risks of data breaches and financial fraud.
- Increasing security awareness – Training employees to recognize social engineering attacks.
For Individuals:
- Privacy protection – Prevents exposure of personal and financial information.
- Avoiding fraud – Reduces the likelihood of falling victim to scams.
Common Social Engineering Techniques
1. Phishing
- Attackers send fake emails or messages with malicious links.
- Goal: Steal login credentials or financial details.
2. Spear Phishing
- A targeted phishing attack aimed at specific individuals (e.g., executives).
- Goal: Gain access to confidential corporate data.
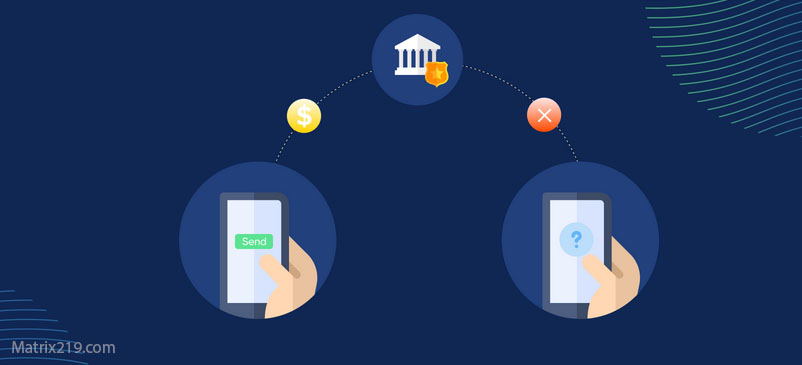
3. Vishing (Voice Phishing)
- Attackers use phone calls to deceive victims.
- Example: Posing as a bank representative to steal account details.
4. Physical Manipulation
- Unauthorized entry into corporate offices to steal data or devices.
- Attackers may impersonate maintenance staff to gain access.
5. Social Media Attacks
- Creating fake profiles to establish trust with victims.
- Goal: Gather personal data for future attacks.
How to Protect Against Social Engineering
1. Awareness & Training
- For Employees: Conduct security awareness programs.
- For Individuals: Learn how to recognize fraudulent schemes.
2. Verify Requests & Sources
- Never share sensitive information without verifying the identity of the requester.
- Avoid clicking on suspicious links or email attachments.
3. Use Security Technologies
- Enable Two-Factor Authentication (2FA) for added protection.
- Keep antivirus and firewall software updated.
4. Limit Publicly Available Data
- Reduce exposure of personal details on social media and public platforms.
5. Create a Security-First Culture
- Encourage employees to report suspicious activities.
Famous Social Engineering Incidents
1. Target Data Breach (2013)
- Attackers tricked a third-party vendor into revealing credentials, compromising millions of customer records.
2. Twitter Hack (2020)
- Employees fell victim to phone-based phishing, leading to the takeover of high-profile accounts.
3. Stuxnet Attack
- Used social engineering tactics to spread malware into industrial control systems.
Conclusion
Social engineering remains a major cybersecurity threat, exploiting human nature rather than technical vulnerabilities. By raising awareness and implementing preventive measures, both individuals and organizations can effectively protect themselves. Security starts with knowledge, and the human factor is the first line of defense.
Source: Read the full article on Matrix219.Net