Social engineering is one of the most dangerous cyber-attack methods, relying on psychological manipulation to target individuals and organizations. Fortunately, these attacks can be mitigated through awareness and effective preventive measures. This article provides a comprehensive guide on how to protect yourself and your organization from social engineering threats.
What is Social Engineering?
1. Definition of Social Engineering
Social engineering refers to psychological manipulation techniques used to deceive victims into revealing sensitive information or granting unauthorized access to systems.
2. Primary Objective
Instead of exploiting technical vulnerabilities, attackers manipulate human weaknesses to infiltrate systems.
Methods of Protection Against Social Engineering
1. Awareness and Education
For Individuals:
- Learn how to identify phishing emails and fraudulent links.
- Understand common social engineering tactics, such as identity impersonation.
For Organizations:
- Conduct regular training sessions to educate employees on social engineering threats.
- Simulate social engineering attacks as part of security training programs.
2. Limiting Available Information
- Reduce the amount of personal or sensitive information shared on social media.
- Regularly review privacy settings to limit access to your data.
3. Implementing Security Technologies
- Two-Factor Authentication (2FA): Adds an extra security layer, even if passwords are compromised.
- Anti-Phishing Software: Install tools that detect and block malicious emails and links.
- Encryption: Use encryption to protect sensitive data at rest and in transit.
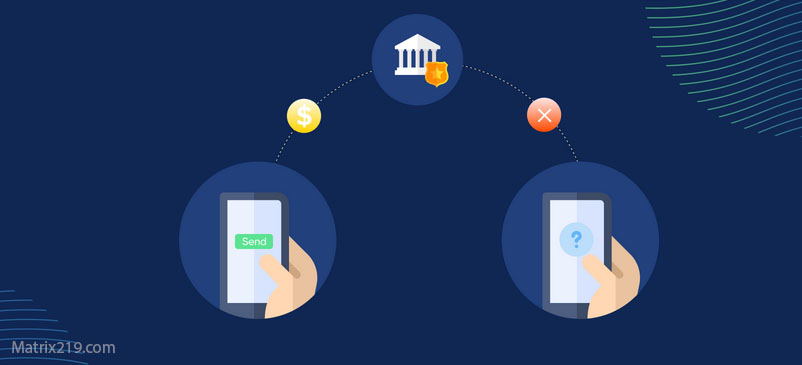
4. Identity Verification
- Do not share personal or sensitive information unless you verify the requester’s identity.
- Confirm that any calls or messages requesting confidential data come from trusted sources.
5. Caution with Links and Attachments
- Verify links before clicking using tools like Google Transparency Report.
- Avoid opening attachments from unknown senders.
6. Security Policies for Organizations
- Establish clear policies prohibiting the sharing of passwords or sensitive data via email or phone.
- Apply the “Principle of Least Privilege (PoLP)” to ensure employees only access necessary information.
7. Emergency Preparedness
- Develop an incident response plan for cyber-attacks, including social engineering threats.
- Ensure a dedicated team is in place to assess damage and implement corrective measures.
Practical Examples of Protection
- Handling Suspicious Emails
- Do not click on links or attachments without verifying the sender.
- Check the sender’s email address for legitimacy.
- Protecting Organizational Data
- Train employees to avoid sharing sensitive work information with unknown entities.
- Regularly review system access logs.
- Enhancing Personal Security
- Avoid using easily guessed passwords.
- Change passwords regularly and do not reuse them across multiple accounts.
Advanced Security Technologies
1. Artificial Intelligence (AI)
- AI-powered systems analyze behavior and detect suspicious activities.
2. Threat Analysis Tools
3. Voice Recognition Technology
- Used to verify callers’ identities in high-security environments, such as banking institutions.
Conclusion
Social engineering targets human vulnerabilities, making awareness and caution the most effective defense strategies. By implementing the recommended precautions—whether as an individual or an organization—you can minimize risks and strengthen the security of your data and systems.
Source: Original Article on Matrix219.Net